Backpack Missiles: The Democratization of Guided Lethality and What It Means for America’s Airspace
Thompson Technologies Defense Intelligence Desk
WASHINGTON March 18, 2026
For decades, the shoulder-fired missile — what the defense community formally designates a Man-Portable Air-Defense System, or MANPADS — represented the absolute floor of state-sponsored lethality. These weapons were serious instruments of national power, requiring serious national resources to produce, maintain, and deploy. The FIM-92 Stinger, America’s iconic Cold War-era warfighter’s companion, costs upward of $480,000 per unit. Even the U.S. Air Force’s experimental low-cost missile program, known as CAMP — launched specifically to address the Pentagon’s growing alarm at the cost disparity between its own munitions and the improvised weapons increasingly deployed against them — is currently targeting a per-launch price point in the same half-million-dollar neighborhood. The barriers of cost, precision manufacturing, classified guidance systems, and controlled propellant chemistry made MANPADS the exclusive province of governments and their proxies. You could not build one in a garage. You could not source the components from consumer channels. The physics and engineering were real, but the access was not.
That era is ending — and it ended faster than most analysts predicted.
This week, a technology hobbyist published a five-minute YouTube video demonstrating a functional shoulder-mounted guided missile prototype built for $96 in off-the-shelf parts and a consumer 3D printer. The creator, Alisher Khojayev, has produced not merely a curiosity, but a proof of concept that will reverberate through aviation security, C-UAS policy, and congressional oversight circles for years to come. The design is complete, the documentation is public, and the barrier is gone.
This is what I call a backpack missile — and it changes everything.
The Convergence That Made This Inevitable
Those of us who have spent years working the counter-UAS policy lane have long warned that the proliferation of enabling technologies — cheap microcontrollers, additive manufacturing, open-source flight control software, commercial GPS, and consumer-grade inertial measurement systems — would eventually collapse the cost barrier separating improvised weapons from military-grade guided munitions. We warned this in policy forums, in congressional briefings, in regulatory comment periods, and in published analyses going back nearly a decade. The response was generally polite acknowledgment followed by institutional inertia. The acquisition community was preoccupied with peer competitors and hypersonic threats. The homeland security apparatus was still calibrating to the basic drone problem. The idea that a garage engineer could build a guided missile was treated as a thought experiment rather than an engineering roadmap.
It was always an engineering roadmap.
What Ukraine’s drone engineers demonstrated with one-way attack platforms is the clearest recent proof: that necessity, combined with access to commercial components, produces weapons innovation at a pace that formal defense procurement cannot match. Ukrainian forces fielded improvised FPV attack drones within months of identifying the tactical requirement, iterating through design generations at a tempo that would take a U.S. defense prime years and hundreds of millions of dollars to replicate. The cost per kill dropped from hundreds of thousands of dollars to hundreds of dollars. The logistics footprint shrank from depot-level sustainment to a backpack and a laptop. The skills required dropped from specialized military training to the competency base of a hobby drone community.
Khojayev’s prototype is the next vector of this same convergence, now applied to the guided missile domain. It was predictable to anyone watching the technology trajectories. It was not, apparently, predicted by the people responsible for regulating it.
The technological ingredients are not exotic. The ESP32 chip family, originally designed for IoT applications and sold for a few dollars at scale, has become the workhorse of the global maker community precisely because it is inexpensive, powerful, capable of wireless communication across multiple protocols, and supported by a vast library of open-source firmware and documentation. The MPU6050 inertial measurement unit was designed for consumer electronics stabilization — for keeping your smartphone screen oriented and your DJI gimbal level. It costs less than two dollars. GPS modules with sub-meter accuracy are available in the same commercial channels that supply hobbyist drone builders. Barometric sensors, compasses, and servo actuators are similarly unremarkable consumer components.
The 3D printing of structural components requires nothing more than a mid-range consumer printer, widely available filament, and an afternoon of machine time. The design files for the printed components are posted publicly. Every component that makes this prototype function is available on Amazon or AliExpress. None of it is on a munitions control list. None of it triggers an export control flag. None of it generates an intelligence signature that would alert a fusion center or a field office to a weapons development program in progress. You could order every component in a single shopping session and have them delivered to any address in the country within 48 hours.
The sophistication of the integration is the only thing that previously stood as a meaningful barrier. That barrier is now documented, open-sourced, and freely downloadable.
The System: What Khojayev Actually Built
Understanding the threat requires understanding the engineering, so it is worth going beyond the headline number and examining what $96 actually buys.
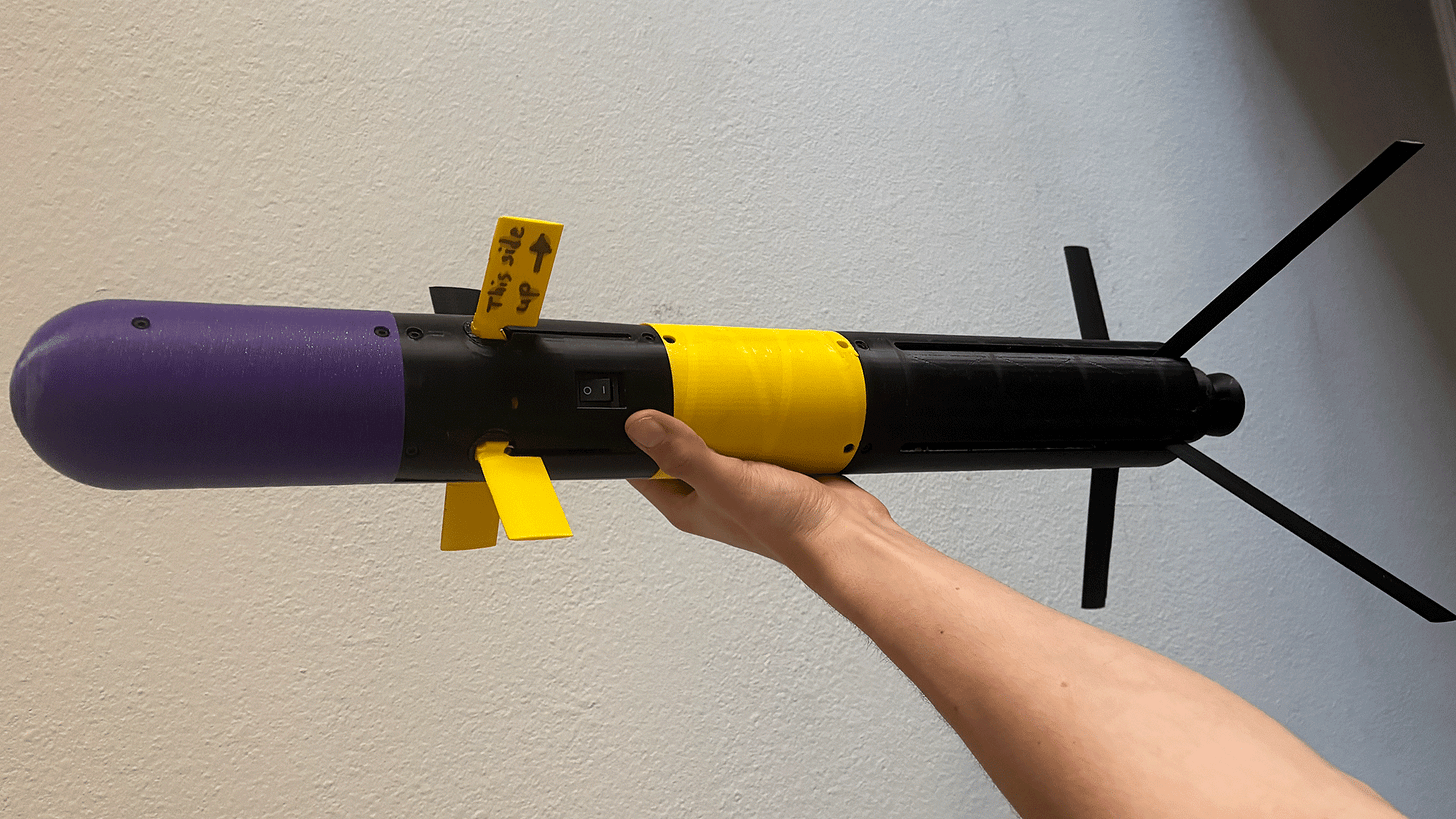
The system Khojayev demonstrated comprises three primary assemblies: the launcher, the missile body, and an optional camera-and-GPS mesh node for extended targeting capability. The structural components of both the launcher and the missile are substantially 3D-printed, using consumer-grade filament materials. The guidance and control electronics are housed within these printed structures and wired using standard hardware store materials — nothing specialized, nothing traceable.
The operational sequence begins when the operator inserts a missile into the launcher and activates the first switch. This action initializes a Wi-Fi network between the launcher assembly and a control computer. The launcher’s ESP32 microprocessor begins exchanging data with the computer, which ingests the rocket’s telemetry and initiates ballistic calculations based on target range, bearing, altitude, and atmospheric conditions. These calculations are relayed back through the Wi-Fi link to the launcher, and from the launcher to the missile, configuring the guidance system prior to launch.
When the operator activates the second switch, the control architecture extends to the missile itself, and orientation angle calculations begin flowing to the missile’s canard actuators — the small movable fins positioned at the forward end of the projectile that provide directional control during flight. The canards respond to guidance commands, steering the missile toward the calculated intercept solution.
The launcher contains an ESP32 microprocessor paired with a GPS receiver, a barometric pressure sensor, and a compass. The missile contains its own ESP32 paired with an MPU6050 inertial measurement unit, which calculates orientation and velocity throughout the flight envelope and drives the canard control surfaces accordingly. The entire guidance loop — from sensor input to actuator response — runs on off-the-shelf consumer hardware costing a combined sum that would not cover a single meal at a Washington, D.C. steakhouse.
The optional camera-and-GPS mesh node extends the system’s capability by providing networked target acquisition and tracking. Khojayev has prototyped this component as well, using the same consumer hardware philosophy. The mesh node concept is particularly significant from a threat assessment standpoint, because it represents the architecture for a networked engagement capability — a distributed sensor-shooter grid that could in principle allow a single operator to engage multiple targets with minimal repositioning. This is not merely a hobbyist toy. This is an embryonic area weapons system.
The entire design, including technical documentation, component lists, wiring diagrams, and printed parts specifications, is publicly posted and freely accessible. The knowledge cannot be unshared.
Why This Matters to Defense Planners
The backpack missile represents a category of emerging threat that existing regulatory, intelligence, and detection frameworks were categorically not designed to address, and the gap between the threat’s current state and the defensive architecture arrayed against it is wider than most decision-makers currently appreciate.
Traditional MANPADS threat analysis has been centered almost exclusively on state proliferation — specifically, the risk of Soviet-era shoulder-fired missiles migrating from post-conflict zones into the hands of terrorist organizations and non-state actors. This was a legitimate and serious concern, and it shaped decades of policy. The Stinger’s documented history in Afghanistan, both as a CIA-supplied mujahideen weapon in the 1980s and as a recovered platform that continued to circulate in regional arms markets for years afterward, made MANPADS proliferation a central pillar of aviation security planning. The 2002 Mombasa attack on an Israeli charter aircraft, which narrowly missed an airliner carrying hundreds of passengers, crystallized the threat into concrete policy action.
The countermeasures developed in response to that threat model were appropriate to the model itself. Aircraft-mounted directed infrared countermeasures, or DIRCM systems, were developed and deployed to defeat heat-seeking MANPADS seekers by blinding or decoying the guidance system. Controlled proliferation agreements between states sought to limit the diffusion of military MANPADS into ungoverned spaces. Post-conflict weapons buyback programs, funded by the State Department and various NGOs, attempted to remove legacy systems from circulation. Intelligence collection against MANPADS trafficking networks became a counterterrorism priority. These were all sensible responses to a well-characterized threat.
Every one of them presupposes a world in which the weapons originate from state arsenals, flow through identifiable logistics chains, and require a degree of technical skill and infrastructure that limits the pool of potential threat actors. Khojayev’s design breaks that assumption at every level. There is no state arsenal to track. There is no trafficking network to interdict. There is no specialized manufacturing requirement that limits the threat actor pool. The weapon is fabricated at the point of use, from components that are functionally invisible to every existing monitoring framework — export controls, financial surveillance, supply chain intelligence, and law enforcement — that our security architecture currently employs.
The threat has shifted from controlled proliferation to distributed fabrication. The policy architecture has not shifted with it.
Equally concerning is the trajectory of the technology itself. Khojayev’s current prototype is an unguided proof of concept in the sense that it lacks a warhead and its guidance effectiveness in a real engagement environment has not been demonstrated. But the gap between a working guidance and control architecture — which he has demonstrably produced — and an operational weapon is not a gap of science. It is a gap of engineering detail and materials access. The guidance problem, historically the hardest part of a missile system to solve, has been solved on a $96 budget. The propulsion and warhead problems are not harder. They are, in certain respects, simpler, and they are similarly well-documented in open-source technical literature.
Defense planners need to internalize that the question is no longer whether non-state actors will have access to guided missile technology. The question is what they will do with it, and how quickly.
The C-UAS Connection
For those of us working in counter-unmanned aircraft systems policy and technology, the backpack missile introduces an uncomfortable recursive problem that has not yet been adequately addressed in the C-UAS community’s analytical and doctrinal literature.
The same proliferation of low-cost commercial airborne platforms that C-UAS doctrine is designed to address — the swarms of cheap commercial UAS being adapted for surveillance, electronic warfare, and kinetic strike applications — is now generating countermeasures that are themselves low-cost, portable, and operating outside traditional weapons control frameworks. The C-UAS community has spent years developing detection, tracking, and defeat systems optimized against commercial quadcopters, fixed-wing gliders, and their military-grade equivalents. The threat taxonomy has matured significantly. The acquisition programs, while still lagging operational need in many respects, are producing capable systems. The regulatory framework for C-UAS authorities, while still incomplete, has advanced meaningfully.
None of that work was designed against a guided missile threat from a non-state actor equipped with commercially sourced components.
If Khojayev’s system, or any of its inevitable successors, were paired with an autonomous or semi-autonomous target acquisition layer — and the computer vision capabilities required for basic airborne target identification are now available in consumer hardware at a price point that makes their incorporation into a $96 weapons system entirely plausible — the resulting system would represent a credible kinetic threat to rotary-wing aircraft operating at low altitude, to unmanned logistics platforms serving forward-deployed forces, to vertical lift assets conducting medevac operations in contested environments, and potentially to commercial aviation assets in terminal airspace near major population centers.
The detection problem is severe and deserves frank acknowledgment. Current airspace security frameworks have no effective mechanism for identifying a backpack missile threat before employment. A traditional MANPADS presents a pre-employment signature: it must be acquired through controlled channels, transported through supply chains, and manned by personnel with some training profile. An intelligence agency with sufficient collection capability against the relevant networks can, in principle, detect the threat before it arrives at the launch point. This has happened. Lives have been saved because of it.
A backpack missile assembled from Amazon deliveries in a private residence generates no equivalent pre-employment signature. There is no acquisition intelligence to collect. There is no training event to observe. There is no transportation movement that generates a pattern of life anomaly. The threat appears, fully formed, at the moment of launch — at which point the defensive window has collapsed to seconds and the range to target may already be inside the engagement envelope of any aircraft in the vicinity.
The implications for National Special Security Event planning, for critical infrastructure airspace protection, and for the emerging Urban Air Mobility sector are significant and underanalyzed. The NSSE community has made substantial investments in ground-based C-UAS capability following the drone incidents over Washington, D.C. in 2023 and 2024. That capability is calibrated to the commercial drone threat. It is not calibrated to a guided surface-to-air engagement, and the sensor architectures, rules of engagement, and command and control frameworks that govern NSSE airspace security were not built with this threat in mind.
This needs to change, and it needs to change before there is an incident that forces the change reactively and at great cost.
The Regulatory Gap
The legal status of a system like Khojayev’s prototype in the United States is genuinely complex, and the complexity is not merely academic — it reflects fundamental tensions in how American law approaches the intersection of fabrication technology, weapons law, and free speech that have not been resolved in the courts or by Congress.
The design file and its constituent components occupy an uncomfortable legal gray zone. The printed structural components, taken in isolation, are not weapons. The ESP32 microprocessors are not weapons. The GPS modules, barometric sensors, and servo actuators are consumer electronics. The Wi-Fi guidance architecture is software, and software — even software that controls weapons systems — has been treated by courts as expression protected by the First Amendment. The assembly of these components into a functional guided projectile without an energetic warhead is, in itself, almost certainly not a federal firearms violation, because the system does not meet the statutory definition of a firearm or a destructive device in the absence of an explosive payload.
The moment an explosive warhead is incorporated, the legal calculus changes dramatically. Under the National Firearms Act, an unregistered destructive device — defined to include missiles equipped with explosive, incendiary, or poison gas warheads above a certain threshold — is a felony in possession. The Arms Export Control Act and the International Traffic in Arms Regulations similarly prohibit the transfer of MANPADS-class systems without State Department authorization. But Khojayev has not published a warhead design. He has published a guidance and control architecture. The enforcement gap between those two things is vast, and navigating it in real time — while a bad actor moves from open-source design to functional weapon — is not something the current legal framework is equipped to do.
Several states have recently moved to regulate 3D printers directly in response to the ghost gun proliferation problem. Colorado has proposed a surveillance requirement for consumer printers. California has sued websites hosting printed firearm design files under civil code theories. New York has proposed sweeping restrictions on 3D printing activities that could produce firearm components. These efforts are legally contested, practically limited in effectiveness, and in any case address only one node of the backpack missile’s production chain. You could build Khojayev’s guidance system without printing a single component, using metal tubing, commercially available hardware, and the same consumer electronics. The 3D printing is a convenience, not a requirement.
The gap in the regulatory framework is not, fundamentally, a gap that more regulation of 3D printers will close. The underlying enabling technologies — cheap microcontrollers, commercial GPS, open-source flight control software, accessible inertial sensors — are too broadly distributed, too deeply embedded in legitimate consumer and commercial applications, and too legally protected to be regulated out of the threat equation. The same chip that guides a backpack missile guides a hobbyist drone, an agricultural automation platform, and an educational robotics kit. You cannot regulate the ESP32 without regulating an enormous swath of the American innovation economy, and no serious policy analyst believes that is a viable path.
The honest regulatory conclusion is that the component-level approach to backpack missile proliferation is a dead end. The policy response must be located downstream, in detection, attribution, and consequence — not upstream, in component access control.
The Cost Asymmetry Problem and What It Means for Golden Dome
The cost disparity highlighted by the Khojayev prototype is not merely a headline-grabbing data point. It is a structural problem that sits at the heart of the United States’ entire layered air defense investment thesis, and it deserves serious analytical attention as Congress and the Department of Defense move forward with the Golden Dome initiative.
The Golden Dome concept — a layered, integrated air and missile defense architecture designed to provide persistent coverage against ballistic missiles, cruise missiles, hypersonic glide vehicles, and UAS threats across the continental United States — is ambitious, necessary, and extraordinarily expensive. The investment required to field a credible Golden Dome capability is measured in hundreds of billions of dollars over decades. The interceptors that comprise its lower tiers — the systems that would be expected to engage cruise missiles, advanced UAS, and MANPADS-class threats in the terminal phase — cost tens of thousands to hundreds of thousands of dollars per engagement.
Against a $480,000 Stinger fired by a state-sponsored proxy, that cost exchange ratio is, while imperfect, defensible. The threat is sophisticated, the supply chain is traceable, the actor pool is limited, and the consequences of miscalculation are severe enough to deter most potential adversaries.
Against a $96 backpack missile assembled from Amazon components, the cost exchange ratio becomes militarily and fiscally incoherent. A determined non-state actor with moderate technical skill, a consumer 3D printer, and $96 in parts can now field a guided surface-to-air weapon. The cost of a layered defense intercept against that weapon will, in virtually any scenario, exceed the weapon’s fabrication cost by orders of magnitude. The attacker can absorb attrition at a rate that the defender cannot sustain economically, and the attacker’s supply chain is so distributed and so deeply embedded in legitimate commerce that supply interdiction is functionally impossible.
This is the same cost asymmetry dynamic that has bedeviled counter-IED operations in Iraq and Afghanistan, that has complicated counter-drone operations in Ukraine, and that is increasingly recognized as a structural feature of the modern threat environment rather than a temporary tactical challenge. The Khojayev prototype represents this dynamic migrating into the guided missile domain. That migration has significant implications for how Golden Dome’s lower tiers are designed, what defeat mechanisms they employ, and how the system is expected to perform in a contested cost environment.
Energy weapons — high-energy lasers and high-power microwave systems — offer the most promising architectural response to the cost asymmetry problem, because their per-engagement cost can, in principle, be measured in dollars rather than thousands of dollars. The U.S. military has been developing directed energy systems for C-UAS and missile defense applications for years, and the technology has matured significantly. But energy weapons have their own limitations: atmospheric conditions degrade performance, engagement geometry constrains effectiveness, power generation requirements complicate forward deployment, and the systems themselves are expensive and maintenance-intensive. They are part of the answer, not the whole answer.
The broader point is that Golden Dome’s architectural assumptions need to account for a threat environment in which guided kinetic weapons can be produced by private individuals at consumer electronics price points. If those assumptions are not updated, the nation risks investing hundreds of billions of dollars in a layered defense architecture optimized against a threat taxonomy that no longer accurately describes the lower end of the threat envelope.
Strategic Implications and the Path Forward
The appropriate policy and operational response to the backpack missile threat is not suppression of the underlying technology. That ship has sailed, the tide is not turning, and any policy framework built on the premise that the enabling technologies can be put back in the bottle is a policy framework that will fail. The response must be built on three foundations: detection, attribution, and consequence — with detection at the center, because without it, the other two are moot.
Detection of the backpack missile threat requires investment in wide-area sensor architectures capable of identifying missile launch events in proximity to critical infrastructure and controlled airspace. Acoustic sensor networks, calibrated to the specific signature of small solid-propellant motors, have demonstrated utility in analogous applications. Electro-optical and infrared sensor coverage of the terminal airspace surrounding NSSE venues, major airports, and critical infrastructure nodes needs to be designed with the backpack missile threat explicitly in its threat model. The current generation of deployed C-UAS sensors is optimized for the radar cross-section, acoustic profile, and radio-frequency emissions of commercial multirotor drones. A small guided missile presents a different signature profile, and the sensor suite needs to evolve accordingly.
Attribution in the backpack missile context means building the forensic and intelligence capability to identify actors who have moved from design file to physical prototype. This is harder than attribution in the traditional MANPADS context, because the production chain is so dispersed and so embedded in legitimate commerce. But it is not impossible. Purchase pattern analysis, combined with behavioral indicators and human intelligence, can surface individuals who are aggregating backpack missile components at scale. The challenge is building the analytical architecture to identify that pattern in real time, before an employment event, rather than reconstructing it forensically afterward.
Consequence means ensuring that the legal framework is robust enough to deter the transition from open-source experimentation to operational weapon, and that law enforcement has the tools and authorities to act before that transition is complete. The current legal framework, as discussed above, has meaningful gaps at the design-and-prototype stage. Those gaps should be addressed legislatively, with appropriate attention to First Amendment implications and without impeding legitimate research and education.
For the C-UAS community specifically, the backpack missile demands integration into the threat library, the training curriculum, and the doctrine that governs how C-UAS operators and first responders assess and respond to airspace security incidents. An operator who is calibrated exclusively to the commercial drone threat will not recognize the acoustic, visual, and electronic signatures of a backpack missile employment event until it is too late. That calibration gap needs to close.
Finally, and perhaps most fundamentally, the defense and homeland security communities need to internalize a cultural shift in how they think about the lower bound of the weapons proliferation problem. The backpack missile is not an anomaly. It is a data point on a trend line that has been moving in one direction for over a decade. The next data point on that trend line will arrive faster than this one did, and it will be more capable. The question is not whether we are surprised. The question is whether we are prepared.
The barrier to guided lethality has not merely been lowered. For practical purposes, at the low end of the threat spectrum, it has been removed. The policy apparatus, the defense acquisition community, and the congressional oversight structure need to reckon with that reality — not in the next authorization cycle, and not after an incident forces the conversation. Now.
Thompson Technologies provides defense intelligence analysis and counter-UAS policy advisory services. The firm’s principals bring aerospace engineering credentials, active congressional relationships, and extensive regulatory experience to the national security technology policy domain. This article is produced for informational and policy research purposes under the Thompson Technologies Defense Intelligence Desk byline.
© 2026 Thompson Technologies / CUAS Coalition LLC. All rights reserved. Reproduction with attribution permitted.